Security & Threat Intelligence
The $10 Hack: Defeating Enterprise Access Control with Canned Air and Cardboard
Your organization spent $50,000 on a state-of-the-art access control system. We bypassed it with a $10 can of compressed air and a piece of cardboard. Total time to bypass: 11 seconds.
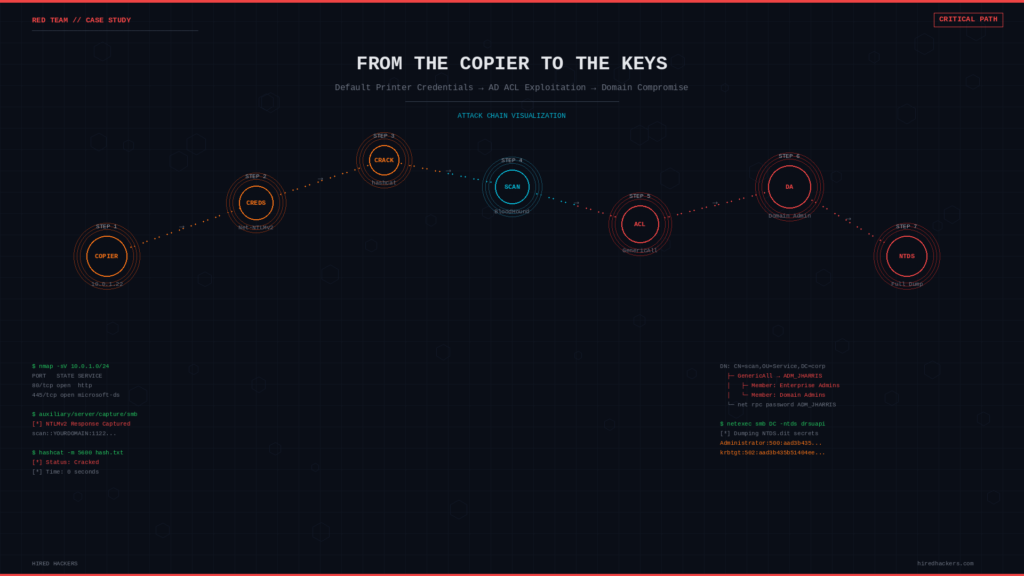
Keys Under the Mat: Recovering Credentials from the Windows Registry
From a single compromised workstation, we dumped LSA secrets and recovered plaintext credentials for 14 service accounts, including one with Domain Admin. No brute forcing. Just reading what Windows kindly stored for us.
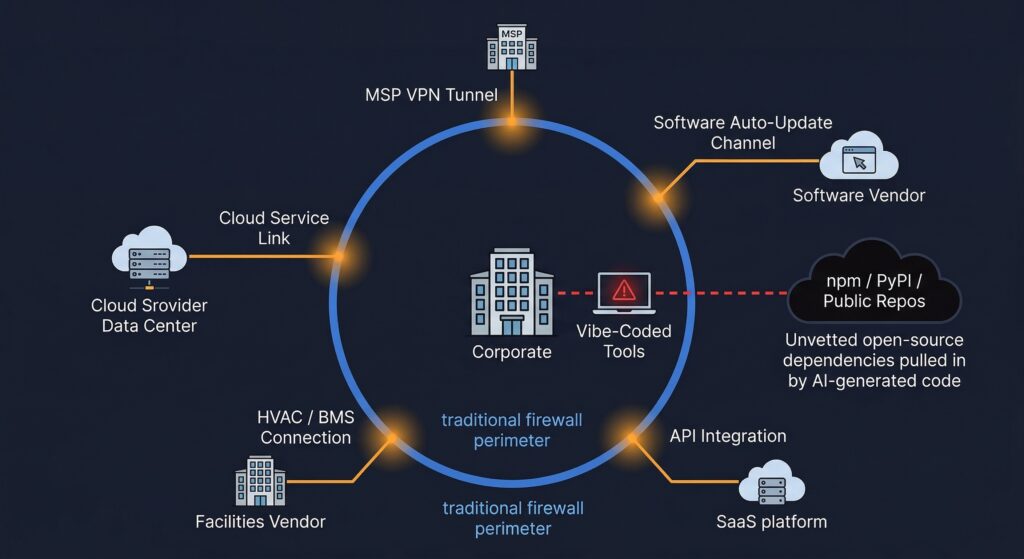
Supply Chain Security: Testing Your Vendors Before Attackers Do
The contractor spent millions on their own security. Their managed service provider spent next to nothing. We pivoted to the MSP and had access to classified documentation within 24 hours.
AI Is Closing the Window. Is Your Patching Program Fast Enough?
The window between vulnerability disclosure and active exploitation has collapsed. Most organizations were already losing the remediation race before AI entered the picture.
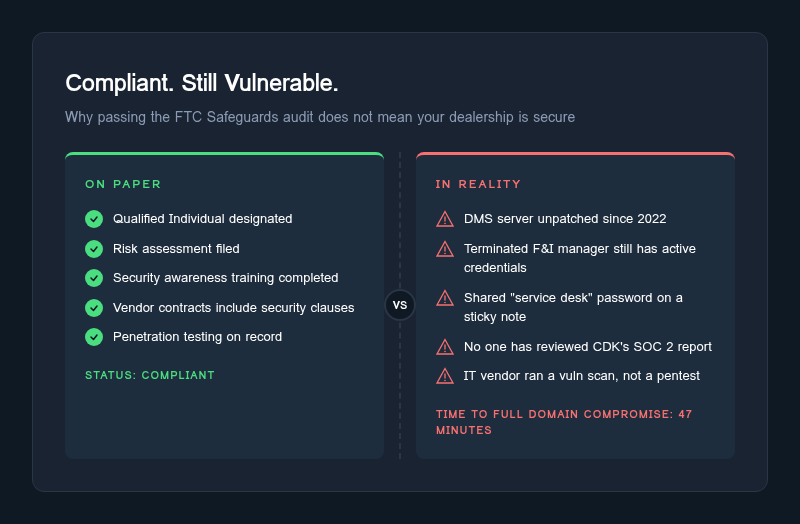
The 9 FTC Safeguards Requirements, Ranked by How Badly Companies Actually Fail Them
Most companies nail the easy FTC Safeguards requirements and crater on the technical ones. Here is how the nine requirements rank by failure rate, based on real assessments.
Your Car Dealership Passed the FTC Safeguards Audit, But Can It Survive a Real Attack?
Passing the FTC Safeguards Rule audit does not mean your dealership is secure. See how compliant dealerships still get breached and what a real penetration test reveals.
From the Copier to the Keys: Default Printer Credentials and AD ACL Misconfigurations
A networked copier with default admin credentials. A stored domain account. Six hops through Active Directory ACL misconfigurations. Complete domain compromise - no CVE required.
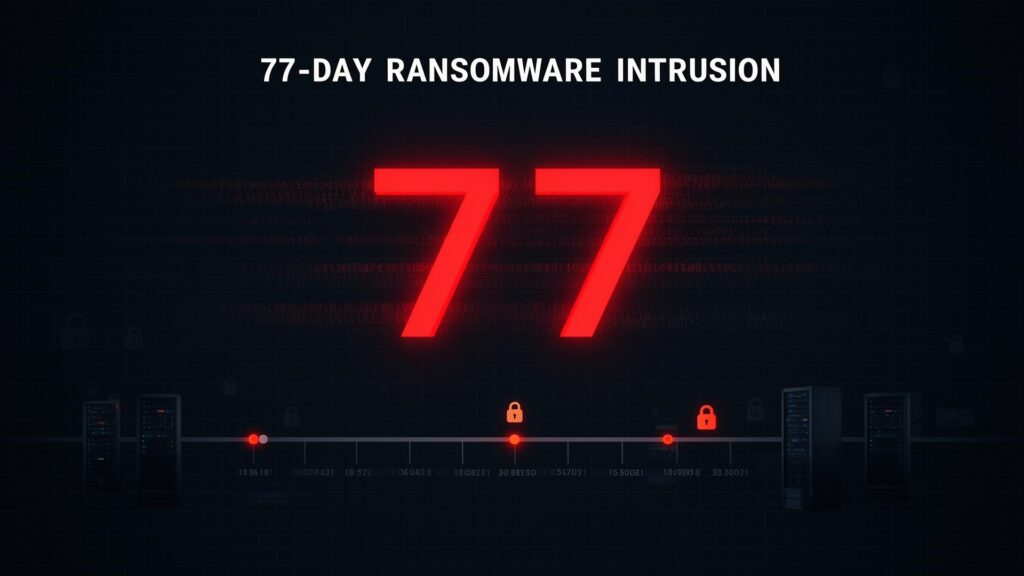
They Were Inside for 77 Days. The Ransomware Was Already Loaded.
77 days of dwell time. Three simultaneous remote access tools on the domain controller. A kernel-level encryption driver reinstalling itself on a weekly schedule. This is the investigation that caught
Mortgage Brokers: The FTC Safeguards Rule Applies to You Too, and the Industry Is Not Ready
The FTC Safeguards Rule applies to mortgage brokers and non-bank lenders with the same requirements and penalties as auto dealers. Most are not compliant.
Microsoft 365 Under Siege: Why Your MFA Isn’t Stopping Session Token Theft
AiTM attacks completely bypass MFA by stealing authenticated session tokens. We demonstrate real-world M365 account takeover in 12 minutes and provide validated remediation strategies.
Beyond the Password: How Session Token Theft Bypasses MFA and What You Can Do About It
Session token theft via AiTM frameworks like Evilginx completely bypasses traditional MFA. We demonstrate real-world Okta account takeover and provide a comprehensive, validated remediation strategy.
OEM Mandate: Mercedes-Benz and the Information Security Shift
Mercedes-Benz requires dealers to implement a qualified information security program by September 30, 2026. ISO 27001 or TISAX Level 2 certification will satisfy the requirement.
The ‘Active Defense’ Doctrine: Moving Beyond Compliance
In 2026, 'being compliant' is the bare minimum. To survive, you must adopt a doctrine of Active Defense.
Threat Landscape 2026: The Era of Autonomous Risks
AI-driven attacks are projected to surge 300%. From 'Vibe Coding' vulnerabilities to agentic malware, here's what security leaders must prepare for in 2026.
Threat Landscape Review 2025: The Year of Automated Exploitation
From AI-weaponized phishing to ransomware's evolution into 'killware,' 2025 marked the shift from human-speed to machine-speed attacks. A comprehensive retrospective on the year's defining threats.
2026 Threat Predictions: What CISOs Need to Know
Based on comprehensive research and our own penetration testing data, here's what security leaders need to prepare for in 2026.
Why Most Purple Team Programs Fail
Most purple team programs fail to deliver real security improvements. We break down the common failure patterns and how to build a program that actually works.
DNS Tunneling: Red Team Tactics and Blue Team Detection
DNS is often an overlooked vector for data exfiltration. Learn how attackers tunnel data through DNS and how to detect this stealthy technique.
The CARS Rule: What Dealers Need to Know After the Fifth Circuit Decision
UPDATE: The FTC's CARS Rule has been vacated by the Fifth Circuit. Here's what dealers need to know about the ruling and what still applies.
CMMC Level 2 Certification: A Realistic 12-Month Timeline
For defense contractors, achieving CMMC Level 2 is a marathon, not a sprint. Here is a realistic 12-month roadmap covering SSP, POA&M, and the C3PAO assessment.
Lessons from a Ransomware Response
A real-world ransomware response case study revealing the critical mistakes organizations make and the practical lessons that can prevent a repeat incident.
DFARS Flow-Down and NIST 800-171: A Guide for Defense Supply Chains
Prime contractors must ensure their subcontractors handle CUI correctly. Understand DFARS flow-down requirements and NIST 800-171 compliance for your supply chain.
Deal Jacket Audits: How AI is Stopping the FTC at the Door
Manual deal jacket audits are slow and inaccurate. AI-driven auditing is the future of dealership compliance.
5 SOC 2 Mistakes That Cost Months
After supporting dozens of organizations through SOC 2 preparation, we've identified five critical mistakes that consistently add months to the audit timeline.
The Most Dangerous Cloud Misconfigurations in 2025
After pentesting hundreds of cloud environments in 2025, we reveal the most dangerous and commonly exploited misconfigurations across AWS, Azure, and GCP.
Red Sea Risk Returns: Renewed Houthi Attacks & Global Shipping
What happened. July 2025 saw renewed Houthi attacks on commercial shipping, including claims of a vessel sinking and follow-on responses such as Greek salvage deployments—evidence that the threat corridor remains live despite earlier multinational actions. Why it...
Double Extortion Ransomware: The Healthcare Threat Landscape
With a 94% data exfiltration rate, groups like RansomHub and BlackCat are aggressively targeting healthcare. Learn about the shift to exfiltration-first tactics.
The “ToolShell” Summer: SharePoint zero-days, real-world fallout, and Microsoft’s new rules
What happened. In mid-July 2025, attackers chained two SharePoint zero-days (CVE-2025-53770/53771), rapidly compromising hundreds of orgs across government, healthcare, and finance. CISA added them to KEV and issued analysis, and Microsoft confirmed active...
Baltic & Eastern Europe GNSS Jamming/Spoofing: Aviation & Maritime Impacts
What happened. Summer 2025 reports show sustained GNSS interference across the Baltic region—researchers identify ship-borne or Kaliningrad-linked jammers; GPS World and Defense News detail the operational impact. EASA/IATA announced a joint plan to mitigate GNSS...
Detection Engineering: A Practical Guide
Detection engineering transforms security monitoring from reactive alert-chasing into proactive threat hunting. Here's how to build, test, and maintain detection rules like software.
The Annual Board Report: Is Your 2025 Plan Ready?
Mid-year is the perfect time to review your security program status before the end-of-year rush.
Kernel Telemetry and ETW: The Future of EDR Detection
As attackers evolve their evasion techniques, defenders must move beyond user-mode hooks. Explore how kernel-level telemetry via ETW provides unbypassable visibility.
Bypassing Modern EDR Solutions: What Defenders Need to Know
Our red team recently demonstrated how sophisticated threat actors can evade endpoint detection. Here's what we learned and how to strengthen your defenses.
Snowflake fallout: why SaaS data platforms are your biggest crown jewels
What happened. In 2025, stolen data linked to the 2024 Snowflake compromises resurfaced in leak-site posts (e.g., Ticketmaster, Santander). Analyses point to weak or missing MFA and stolen credentials rather than a Snowflake platform exploit—reminding teams that...
Tariffs and Pricing: The New Compliance Challenge
As economic policies shift and tariffs impact vehicle costs, dealers must be hyper-vigilant about advertising accuracy.
Drones Are Now a Domestic Security Variable: Airports, Stadiums, and the BVLOS Shift
What happened. Drone incursions near U.S. airports and stadiums climbed again this summer, prompting federal alarm and new testing of detection tech; FAA says it still fields 100+ airport-near reports monthly and ran new detection trials, while Reuters reported...
HIPAA Security Risk Assessment: A Practical 2025 Guide
Healthcare organizations face increasing scrutiny from OCR. Here's how to conduct a thorough security risk assessment that satisfies regulators and actually improves security.
Why We Don’t Sell Templates: Our Philosophy on Real Security
We are often asked for a 'simple template.' Here is why we refuse to sell them.
Threat Landscape Update: Q1 2025
From AI-powered phishing to supply chain compromises, here's what our threat intelligence team is tracking this quarter.
Building an Effective Purple Team Program from Scratch
Purple teaming bridges the gap between offense and defense. Here's our methodology for building programs that actually improve security outcomes.
MITRE D3FEND: A Practical Guide to Mapping and Strengthening Your Cyber Defenses
Most security teams know MITRE ATT&CK. Fewer know its defensive counterpart: D3FEND. Learn how to use this framework to identify coverage gaps, evaluate vendor claims, and systematically strengthen yo
Penetration Testing vs. Vulnerability Scanning: Know the Difference
The FTC requires both. If you think they are the same thing, you are failing your security audit.
Change Healthcare: the breach that keeps rippling through U.S. healthcare
What’s new. After the 2024 ALPHV/BlackCat attack, 2025 notices show continued remediation and consumer support windows (including deadlines for credit monitoring enrollment). HHS’s FAQ and Change Healthcare’s updates outline impacts and assistance programs as the...
SEC Cybersecurity Disclosure Rules: What Boards Need to Know
The SEC's new cybersecurity disclosure requirements are now in effect. Here's what public companies need to understand about material incident reporting.
Google’s Truth-in-Pricing: The End of ‘Lead with the Rebate
Google has implemented new transparency rules for auto ads, effective October 28, 2025. If your online price doesn't match the deal jacket, your ads are going dark.
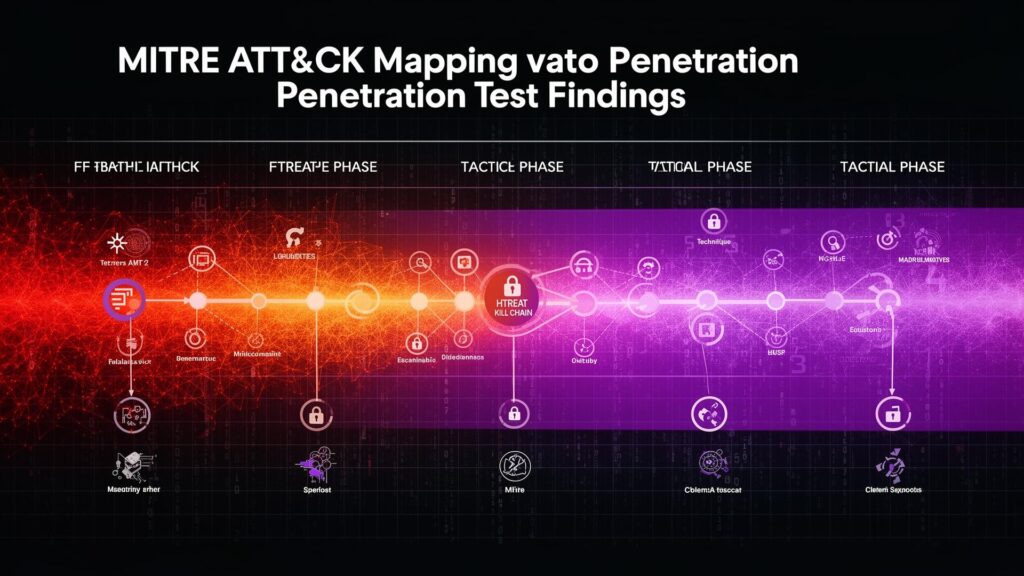
MITRE ATT&CK for Practitioners: How to Map Real Findings to a Common Threat Language
ATT&CK mapping transforms isolated pentest findings, vulnerability scan results, and incident timelines into a structured, measurable view of adversary behavior. This practical guide walks through a r
The ‘100% Solution’ Myth: Why You Must Audit Your Cybersecurity Vendor
In the rush to satisfy federal regulations, a dangerous sales pitch has taken hold: 'Buy our solution, and you are 100% FTC compliant.' It sounds reassuring. It is also legally impossible and operationally reckless.
The ‘Senior Officer’ Requirement: Is Your Board in the Loop?
The FTC requires a written report to be presented to your governing body at least once a year. Here is what needs to be in it.
Vendor Risk Management: Your Third-Party is Your Weakest Link
16 CFR § 314.4(f) requires you to oversee your service providers. If they fail, you fail.
Wiretapping Lawsuits: Are Your Website Pixels Illegal?
A wave of lawsuits is targeting businesses for using tracking pixels like Meta Pixel and CAPI. Your marketing strategy might be a legal liability.
BladeOne News
Bryan County awards BladeOne Cyber Services Contract (ECS Elite)
What happened. Bryan County recommended awarding BladeOne the Enterprise Cybersecurity Solution (ECS) — Elite contract funded by a $193,643 GEMA State & Local Cybersecurity Grant, with a not-to-exceed amount of $224,664. The RFP (issued May 22, 2025; due June...
Media Inquiries
Timely, expert analysis on the record or on background.
BladeOne provides threat-informed commentary and briefings across Strategy, Intelligence, Cyber, Influence, Logistics, and Labs. If you’re covering an active issue or need context fast, our media desk will route you to the right operator.
Primary contact: press@bladeone.com
Urgent (breaking news): use subject line URGENT: MEDIA and include deadline/time zone.
What we can provide
-
Interviews & quotes on ransomware, supply-chain breaches, cloud/SaaS risk, OT/ICS, AI safety, counter-disinformation, executive protection logistics, and C-UAS.
-
Rapid briefings & fact checks with plain-English explainers, diagrams, and verified timelines.
-
Incident context (what’s signal vs. noise), attacker TTPs mapped to ATT&CK, and recommended mitigations.
-
Field perspective on site advance, secure asset logistics, GNSS interference, and crisis communications.