Your organization spent $50,000 on a state-of-the-art access control system. We bypassed it with a $10 can of compressed air and a piece of cardboard. Total time to bypass: 11 seconds.
Cyber News
Keys Under the Mat: Recovering Credentials from the Windows Registry
From a single compromised workstation, we dumped LSA secrets and recovered plaintext credentials for 14 service accounts, including one with Domain Admin. No brute forcing. Just reading what Windows kindly stored for us.
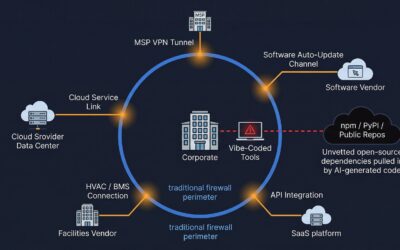
Supply Chain Security: Testing Your Vendors Before Attackers Do
The contractor spent millions on their own security. Their managed service provider spent next to nothing. We pivoted to the MSP and had access to classified documentation within 24 hours.
AI Is Closing the Window. Is Your Patching Program Fast Enough?
The window between vulnerability disclosure and active exploitation has collapsed. Most organizations were already losing the remediation race before AI entered the picture.
The 9 FTC Safeguards Requirements, Ranked by How Badly Companies Actually Fail Them
Most companies nail the easy FTC Safeguards requirements and crater on the technical ones. Here is how the nine requirements rank by failure rate, based on real assessments.
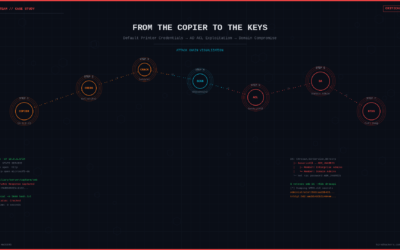
From the Copier to the Keys: Default Printer Credentials and AD ACL Misconfigurations
A networked copier with default admin credentials. A stored domain account. Six hops through Active Directory ACL misconfigurations. Complete domain compromise – no CVE required.