When the FTC Safeguards Rule gets coverage in trade press, the conversation almost always centers on auto dealerships. The auto industry has a loud lobbying presence, a well-organized dealer association, and a history of FTC enforcement activity. Dealers know the rule exists because their compliance vendors won’t let them forget it.
Mortgage brokers and independent lenders are a different story.
The FTC Safeguards Rule applies equally, with the same technical requirements, the same penalties, and the same enforcement authority, to independent mortgage brokers, non-bank mortgage lenders, mortgage servicers, and related financial companies that fall under FTC jurisdiction. And in the mortgage industry, awareness is lower, compliance programs are thinner, and the data at risk is arguably more sensitive than anything on a dealer’s DMS.
If you’re an independent mortgage broker or small non-bank lender and you haven’t built a Safeguards-compliant security program, you’re exposed. This post explains why and what it takes to get right.
Why Mortgage Companies Are a Priority Target
A mortgage file is one of the most data-rich documents in existence. A single loan application contains the borrower’s full name, date of birth, Social Security number, employment history, income documentation, bank statements, tax returns, credit history, and property information.
That’s everything a threat actor needs to commit identity theft, tax fraud, synthetic identity fraud, and account takeover, all in a single file.
For context: a stolen credit card sells for a few dollars on dark web markets. A full identity profile, the kind contained in a single mortgage application, sells for $40 to $200 or more depending on the credit profile. A mortgage broker or small lender processing 30 applications per month is holding hundreds of complete identity packages.
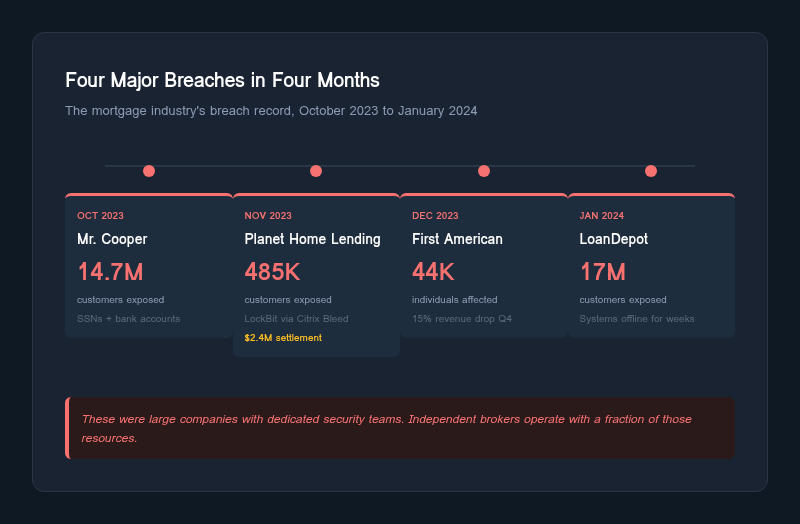
Attackers know this. The mortgage and title industry has been a consistent ransomware target. In late 2023 and early 2024 alone, four major incidents hit the industry:
- Mr. Cooper (Nationstar Mortgage): On October 31, 2023, attackers breached Mr. Cooper’s systems, exposing data on approximately 14.7 million current and former customers. Compromised data included Social Security numbers and bank account information. The sheer volume of affected individuals made this one of the largest mortgage-related breaches on record.
- First American Financial: In December 2023, a ransomware attack took First American’s systems offline, disrupting real estate and title closings nationwide. Approximately 44,000 individuals were affected. The operational impact was severe: the company reported a 15% revenue decrease in Q4 2023 as systems remained down and closings stalled.
- Planet Home Lending: In November 2023, the LockBit ransomware group exploited the Citrix Bleed vulnerability (CVE-2023-4966) to breach Planet Home Lending, affecting approximately 485,000 customers. The incident resulted in a $2.4 million class-action settlement in May 2024, a cost that would be existential for a smaller lender.
- LoanDepot: In January 2024, a ransomware attack took origination systems offline for weeks and exposed data on nearly 17 million customers. Loan officers could not process applications. Borrowers could not make payments through normal channels. The operational disruption alone cost the company tens of millions before accounting for remediation, legal exposure, and regulatory scrutiny.
These are large companies with dedicated security teams. Independent brokers and small lenders operate with a fraction of those resources, which makes them softer targets.
The Regulatory Landscape: Who Covers What
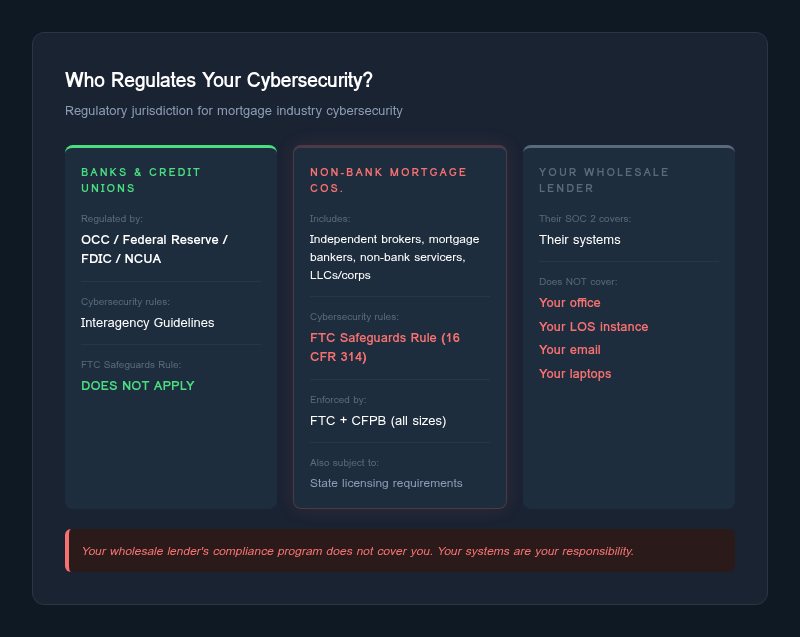
This is where mortgage professionals often get confused, and the confusion creates dangerous compliance gaps.
Banks and federally chartered credit unions are supervised by federal banking regulators: the OCC, Federal Reserve, FDIC, or NCUA. Their cybersecurity requirements come through their respective prudential regulators, not the FTC.
Non-bank mortgage companies, including independent mortgage brokers, mortgage bankers operating as LLCs or corporations, non-bank servicers, and similar entities, are financial institutions under the Safeguards Rule because they are significantly engaged in financial activities. Because they are not supervised by federal banking regulators, the FTC serves as their enforcing authority. For most independent and boutique operations, the FTC Safeguards Rule is the primary federal cybersecurity obligation.
State-level licensing adds requirements on top of this. The CFPB also has supervisory authority over all non-bank mortgage companies regardless of company size under Dodd-Frank Section 1024. But the baseline federal cybersecurity floor for most independent operations is the FTC Safeguards Rule.
The confusion that creates the gap: Many independent mortgage brokers assume that because they operate under state licenses and maintain relationships with correspondent lenders or wholesale investors, those entities’ compliance programs cover them. They don’t. Your wholesale lender’s SOC 2 report covers their systems. Your office, your LOS instance, your email, your document storage, your laptops: that is your responsibility.
What the FTC Safeguards Rule Requires, Applied to Mortgage
The Safeguards Rule was amended in December 2021. The prescriptive technical requirements took effect on June 9, 2023. Additionally, the FTC’s breach notification requirement (notify the FTC within 30 days for breaches affecting 500 or more customers) took effect on May 13, 2024. These are not aspirational guidelines. They are specific, enforceable mandates. Here is how the key provisions apply to mortgage operations:
Written Information Security Program
You need a written, documented security program tailored to your business. Not a generic template downloaded from a compliance vendor’s website. The program must address the specific risks you face: how you receive loan applications, where you store documents, who has access to your LOS, how borrower data moves between your systems and your investors or aggregators.
Designated Qualified Individual
Someone must own the security program. This can be an employee or an outside service provider. For a 5-person brokerage, outsourcing this role is perfectly acceptable under the rule, but it must be a real engagement with actual oversight, not a name on a document.
Risk Assessment
You must conduct and document a risk assessment that identifies reasonably foreseeable risks to customer information. For mortgage companies, this means evaluating risks to your loan origination system, your document management, your email (which almost certainly contains borrower PII), your CRM, any cloud storage, and physical files if you still maintain them.
The risk assessment must be written. It must be updated. And it must drive your security decisions. This is the document the FTC will ask for first in any investigation.
Access Controls
Only authorized individuals should have access to customer information, and only the minimum access required for their role. In practice, this means your processors should not have admin access to your LOS. Your marketing staff should not be able to pull borrower SSNs. Shared logins are a violation.
Encryption
Customer information must be encrypted both in transit and at rest. If you’re emailing loan documents as unencrypted PDF attachments, that’s a gap. If your document storage doesn’t encrypt files at rest, that’s a gap. If your LOS database isn’t encrypted, that’s a gap.
Multi-Factor Authentication
MFA is required for accessing customer information. This applies to your LOS, your email, your document storage, your CRM, and any remote access to your network. SMS-based MFA is better than nothing but is not recommended; authenticator apps or hardware keys are the standard.
Pentesting and Vulnerability Assessments
The rule requires either annual pentesting with semi-annual vulnerability assessments, or continuous monitoring. For most mortgage companies, the annual pentest plus vulnerability scanning approach is the practical path. This is not optional. It is a specific requirement in the amended rule.
Incident Response Plan
You must have a documented incident response plan. Given the breach notification requirement that took effect May 13, 2024, this plan must now include specific procedures for notifying the FTC within 30 days of discovering a breach affecting 500 or more customers.
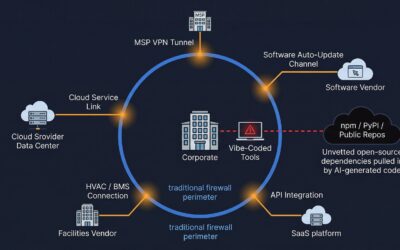
Vendor Management
If service providers have access to customer information, you are responsible for ensuring they maintain appropriate safeguards. Your LOS vendor, your document management provider, your IT support company, your cloud storage provider: all of them need to be assessed and monitored.
Board Reporting
The Qualified Individual must report at least annually to the board of directors or governing body. For a sole proprietor or small LLC, this means a documented annual review of the security program’s status.
Where the Mortgage Industry Is Failing
Based on what we see during assessments and what publicly available enforcement and breach data reveals, the mortgage industry has specific, predictable failure patterns:

Email Is the Biggest Exposure
Mortgage professionals live in email. Loan applications, W-2s, bank statements, 1003 forms, closing documents: the volume of sensitive borrower data flowing through email inboxes is staggering. Most independent brokers use Microsoft 365 or Google Workspace with default configurations. No DLP rules. No encryption policies for outbound attachments. No retention policies aligned with the sensitivity of the data.
When an email account is compromised through phishing (and it happens constantly in this industry), the attacker gains access to years of borrower PII sitting in the inbox and sent folders.
LOS Security Is Assumed, Not Verified
Loan origination systems like Encompass, Calyx, and Byte are critical infrastructure for mortgage companies. Most brokers assume that because the LOS vendor has security certifications, their own instance is secure. That assumption ignores how the system is configured, who has access, whether MFA is enforced on login, whether API integrations are secured, and whether audit logging is enabled and reviewed.
The LOS is the crown jewel. It should be treated like one.
No Formal Risk Assessment Exists
This is the single most common gap we encounter. Independent mortgage brokers frequently have no written risk assessment at all. Some have a generic questionnaire completed for a wholesale lender’s due diligence process, but that is not what the FTC requires. The Safeguards Rule requires a risk assessment specific to your organization, your systems, and your data flows.
Without a risk assessment, every other control is unmoored. You cannot demonstrate that your security program is “based on” an assessment of identified risks, which is the foundational requirement of the rule.
Physical Security Is Overlooked
Many independent brokers operate from small offices, home offices, or shared workspaces. Loan files printed for closings sit on desks. Filing cabinets are unlocked. Visitors can see screens displaying borrower information. These are real risks that must be addressed in the security program.
Vendor Oversight Is Nonexistent
Most mortgage brokers cannot produce a list of vendors who have access to customer information, let alone evidence that those vendors maintain appropriate security controls. The interconnected nature of the mortgage ecosystem, with data flowing between originators, processors, underwriters, title companies, appraisers, and servicers, makes vendor management both critical and complex.
The Enforcement Trajectory
The FTC has been methodical in its approach to Safeguards Rule enforcement. The agency started with auto dealers because the industry is large, the compliance gaps are well-documented, and early enforcement actions create precedent that applies across all covered industries.
Mortgage companies should expect the same trajectory. Several factors make enforcement against non-bank mortgage companies increasingly likely:
The CFPB connection: The CFPB supervises all non-bank mortgage companies regardless of size under Dodd-Frank Section 1024. CFPB examinations can identify cybersecurity gaps that get referred to the FTC for Safeguards Rule enforcement. The two agencies have a history of coordination.
Breach notification as a trigger: Since May 13, 2024, breaches affecting 500 or more customers must be reported to the FTC within 30 days. Every breach report is a potential enforcement investigation. The FTC’s first question will be: “Show us your written risk assessment and information security program.” If you can’t produce them, you’ve effectively admitted to a violation.
State AG activity: State attorneys general have independent authority to enforce consumer protection laws, and many have been increasingly active on data security. A mortgage broker breach that hits local news can trigger a state AG investigation that runs parallel to, or feeds into, federal enforcement.
Consent orders set precedent: Every FTC consent order against an auto dealer for Safeguards Rule violations is a precedent that applies with equal force to mortgage companies. The requirements are identical. The only question is when, not whether, enforcement shifts to other covered industries.
Where to Start If You’re Behind
If you’re an independent mortgage broker or small non-bank lender reading this and recognizing gaps, here is a practical starting point:
1. Conduct a Written Risk Assessment
This is the foundation. Identify the systems that store, process, or transmit customer information. Identify the threats to those systems. Evaluate the sufficiency of your current controls. Document everything. This doesn’t need to be a 200-page report, but it must be specific to your operations and defensible under scrutiny.
2. Designate Your Qualified Individual
If you don’t have an internal security expert (most small brokerages don’t), engage an outside service provider to fill this role. Make sure the engagement includes actual oversight of your security program, not just a name on a compliance form.
3. Lock Down Email
Enable MFA on all email accounts. Implement encryption for outbound messages containing borrower data. Set retention policies. Review forwarding rules (compromised accounts frequently set up silent forwarding to external addresses). Consider a secure document portal as an alternative to emailing sensitive files.
4. Review LOS Configuration
Audit user access in your loan origination system. Remove inactive accounts. Enforce MFA. Review API integrations. Enable and review audit logs. Confirm that encryption is enabled for data at rest and in transit.
5. Build Your Incident Response Plan
Document what you’ll do when (not if) a security incident occurs. Include specific notification timelines for the FTC (30 days for breaches affecting 500+ customers), state regulators, and affected individuals. Run a tabletop exercise at least once a year.
6. Get a Pentest and Vulnerability Assessment
The rule requires it. Annual pentesting combined with semi-annual vulnerability assessments is the standard path to compliance. This should cover your external-facing systems, internal network, web applications, and any cloud services where customer data resides.
7. Document Your Vendor Management
Create an inventory of every service provider with access to customer information. Assess their security posture. Include security requirements in your contracts. Review their compliance annually.
The Bottom Line
The FTC Safeguards Rule is not an auto dealer regulation. It is a financial institution regulation, and non-bank mortgage companies are squarely within its scope. The rule was amended in December 2021 with prescriptive technical requirements that took effect June 9, 2023. The breach notification requirement followed on May 13, 2024. The compliance deadline has passed. The enforcement infrastructure is in place.
The mortgage industry handles some of the most sensitive consumer financial data in existence. The breach examples from 2023 and 2024 demonstrate that attackers already know this. Whether you’re a one-person shop or a regional brokerage with 50 loan officers, the requirements are the same.
The question is not whether the FTC will turn its attention to mortgage companies. It’s whether you’ll be ready when it does.